Resources
Stay in the know with the latest industry events and expert thought leadership on cybersecurity, risk, and compliance.
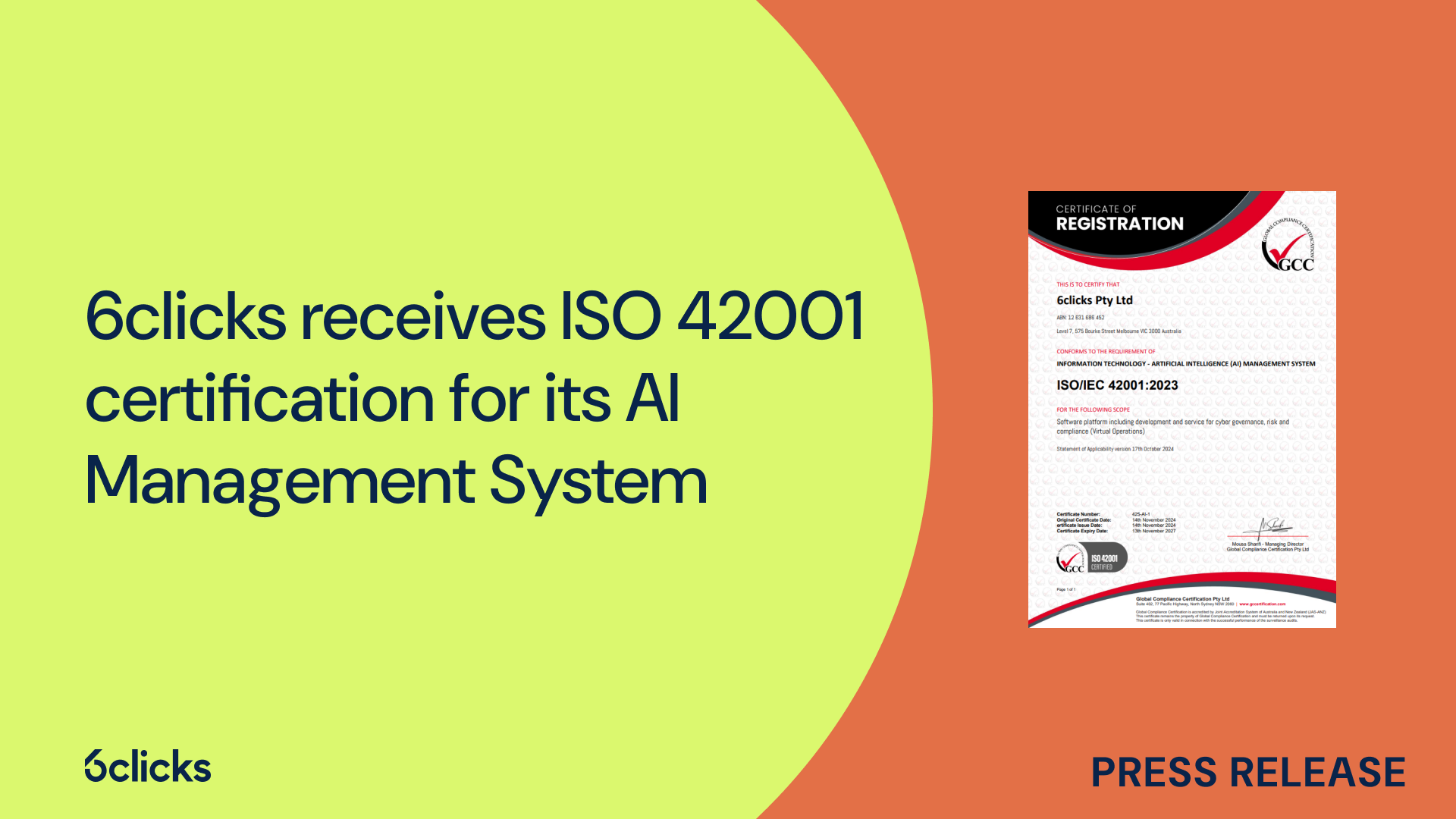
6clicks receives ISO 42001 certification for its AI Management System
6clicks, pioneer of the first AI-powered GRC (Governance, Risk, and Compliance) software, is proud to announce that it has achieved an ISO/IEC 42001 certification for its Artificial Intelligence Management System (AIMS). This certification demonstrates 6clicks' commitment and capability to enhance cybersecurity, risk management, and compliance through robust, resilient, and responsible AI solutions.
Learn moreLatest resources
Discover how 3 Lights, a trusted Australian GRC cybersecurity advisory firm, helps...
Join Andrew Robinson, Chief Information Security Officer & Co-Founder of 6clicks, as...
6clicks is excited to announce the Middle East segment of our No Complexity tour, a...
Popular resources
Cybersecurity is no longer just a technical function—it’s a critical driver of...
Discover how to implement the NIST Cybersecurity Framework with ease. This free...
Get instant access to our comprehensive guide on scaling advisory and managed...
Non-compliance can cost businesses more than just fines. This whitepaper breaks down...
This whitepaper will guide you through the various national and sector-specific...
Streamline your compliance with ISO 42001 and seamlessly align with global standards...
All blogs
Melbourne, Australia – May 7, 2025. 6clicks, the leading AI-powered GRC platform,...
Tokyo, Japan – May 6, 2025. 6clicks, the AI-powered cyber GRC platform, today...
Dubai, United Arab Emirates – May 2, 2025. 6clicks, a global leader in AI-powered...
Intelligently accelerate your cyber risk and compliance program today

Subscribe to receive all the latest updates
Subject to 6clicks Privacy Policy, you agree to allow 6clicks to contact you via the email provided for scheduling and marketing purposes.