Vendor Risk Management
Implement a robust and defensible assessment process for your third-party suppliers and manage risks across your supply chain.
The Benefits
Develop a secure and reliable supplier assessment process, safeguarding against compliance and ethical risks that can damage reputation.
Proactively manage your reputational risk
Automate the monitoring of third-party entities to protect your organization from legal, financial and reputational risk, highlighting issues as they arise.
Actively support business growth
Drive growth and increased revenue for your organization with robust third-party screening and custom due-diligence questionnaires, and risk analysis.
Easily onboard & monitor third parties
Systemize the onboarding and monitoring of third parties with an intuitive, scalable platform that automates compliance processes and keeps pace with the evolving regulatory landscape.
See how 6clicks helps organizations manage risk across their entire supply chain.
The Features
Powerful features to support your growth
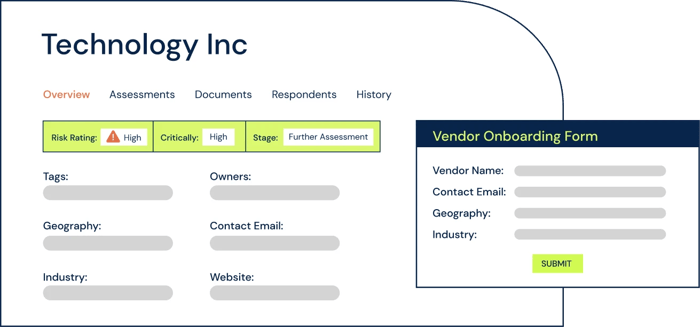
The 6clicks Third-Party module is built for vendor risk management and managing your third parties. With custom business-facing onboarding forms, bulk and automated assessment capability, and workflows, 6clicks has everything you need to identify and manage risks and areas of non-compliance across your third-party ecosystem.
Vendor assessment questionnaires
Create custom vendor assessments or download from the 6clicks Content Library and send them to your third parties.
Vendor risk profiling
Assess the risk associated with your vendors and categorize and group them based on your desired framework.
Vendor onboarding
Bulk add your vendors, and bulk send them assessments. Allow business team members to add vendors via a custom onboarding form with automated assessments.
Documentation and evidence collection
Automate the collection of documents and evidence of compliance from your vendors and store them centrally in 6clicks.
Audit & history logs
Keep track of all changes to your vendors via the vendor history trail. See who changed what and when the change occurred.
Custom fields
Create custom vendor fields to capture the correct information and ensure alignment with your vendor management processes.
Plus, there's unlimited:
-
User licensing across all plans
-
Access to our content library
-
World-class customer support
Why businesses and advisors choose 6clicks
It's faster, easier and more cost effective than any alternative.

Powered by artificial intelligence
Experience the magic of Hailey, our artificial intelligence engine for risk and compliance.

Unique Hub & Spoke architecture
Deploy multiple teams all connected to a hub - perfect for federated, multi-team structures.
Fully integrated content library
Access 100's of standards, control sets, assessment templates, libraries and playbooks.
Featured resources
Featured resources
Intelligently accelerate your cyber risk and compliance program today
Stop wasting time with complicated pricing, longwinded consulting efforts and outdated technology.
